搜索结果: 16-30 共查到“国际动态 计算机网络”相关记录140条 . 查询时间(2.117 秒)

《网络与信息安全学报》被Scopus数据库收录
网络与信息安全学报 Scopus数据库
2022/7/21
俄罗斯拟建超级计算机网络
俄罗斯 超级计算机 网络
2020/2/14
据美国《新闻周刊》网站近日报道,俄罗斯总统弗拉基米尔・普京表示,俄罗斯计划很快在全俄安装多台新型超级计算机,改善俄罗斯超级计算机研制落后于中国和美国的现状。普京近日在访问切雷波夫斯化学技术学院时说,俄罗斯计划扩大由超级计算机和数据中心组成的高科技网络的规模,且该网络将不再局限于首都莫斯科。

New approach for modern power grids increases efficiency, reduces costs(图)
New approach modern power increases efficiency reduces costs
2019/10/17
Modern power grids are rapidly developing because of the increasing availability of renewable energy sources such as solar photovoltaic and wind power. The trend is expected to continue.Renewable ener...
Cyber Corps:Scholarship For Service Recognizes First Hall Of Fame Recipients
Cyber Corps Scholarship Service First Hall Fame Recipients
2018/1/31
The National Science Foundation's (NSF) CyberCorps: Scholarship for Service (SFS) program today announced its inaugural class of SFS Hall of Fame recipients, recognized for making outstanding contribu...
Follow The Bitcoin To Find Victims Of Human Trafficking
the bitcoin victims human trafficking
2017/9/5
A team of university researchers has devised the first automated techniques to identify ads potentially tied to human trafficking rings and link them to public information from Bitcoin ― the primary p...

With cyberattacks on 3D printers likely to threaten health and safety, researchers at Rutgers University-New Brunswick and Georgia Institute of Technology have developed novel methods to combat them, ...
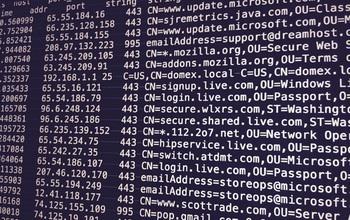
Network Traffic Provides Early Indication of Malware Infection
Network Traffic Early Indication Malware Infection
2017/7/20
By analyzing network traffic going to suspicious domains, security administrators could detect malware infections weeks or even months before they're able to capture a sample of the invading malware, ...

Under Cyber Attack:UH Researchers Look at How to Catch a ‘Phisher’(图)
Under Cyber Attack UH Researchers Phisher
2017/7/20
As cybersecurity experts scramble to stop another wave of ransomware and malware scams that have infected computers around the world, computer science experts at the University of Houston are “phishin...
Whether a nation should retaliate against a cyber attack is a complicated decision, and a new framework guided by game theory could help policymakers determine the best strategy.The "Blame Game" was d...
Novel technique tracks more web users across browsers
Novel technique tracks more web users across browsers
2017/3/13
For good or ill, what users do on the web is tracked. Banks track users as an authentication technique, to offer their customers enhanced security protection. Retailers track customers and potential c...
Reliability measures of electrical grid has risen to a new norm as it involves physical security and cybersecurity. Threats to either can trigger instability, leading to blackouts and economic losses....
Your 'anonymized' web browsing history may not be anonymous
anonymized web browsing history may not be anonymous
2017/2/16
Raising further questions about privacy on the internet, researchers from Princeton and Stanford universities have released a study showing that a specific person's online behavior can be identified b...
Cyberattacks on corporations, agencies, national infrastructure and individuals have exposed the fragility and vulnerability of the internet and networked systems. Achieving truly secure cyberspace re...
This century, our world will be flooded with hundreds of billions of smartphones, gadgets, sensors and other smart objects connected to the internet.They will perform myriad services, such as mon...


